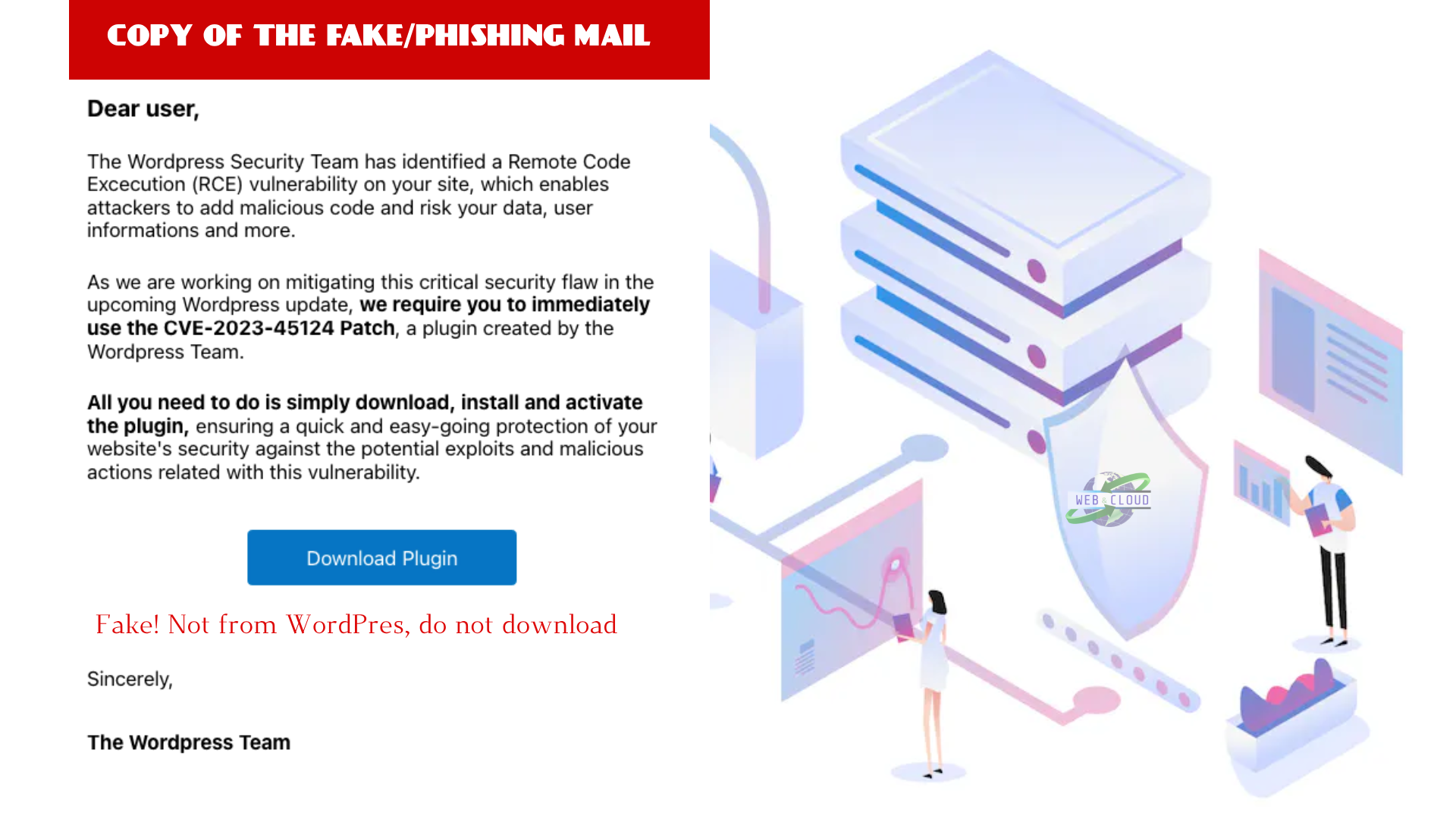
WordFence reports on the fake CVE-2023-45124 Phishing Scam used to force WordPress users to install malware
The Wordfence Threat Intelligence Team has recently been informed of a phishing campaign targeting WordPress users. The Phishing email claims to be from the WordPress team and warns of a Remote Code Execution vulnerability on the user’s site with an identifier of CVE-2023-45124, which is not currently a valid CVE. The email prompts the victim to download a “Patch” plugin and install it.
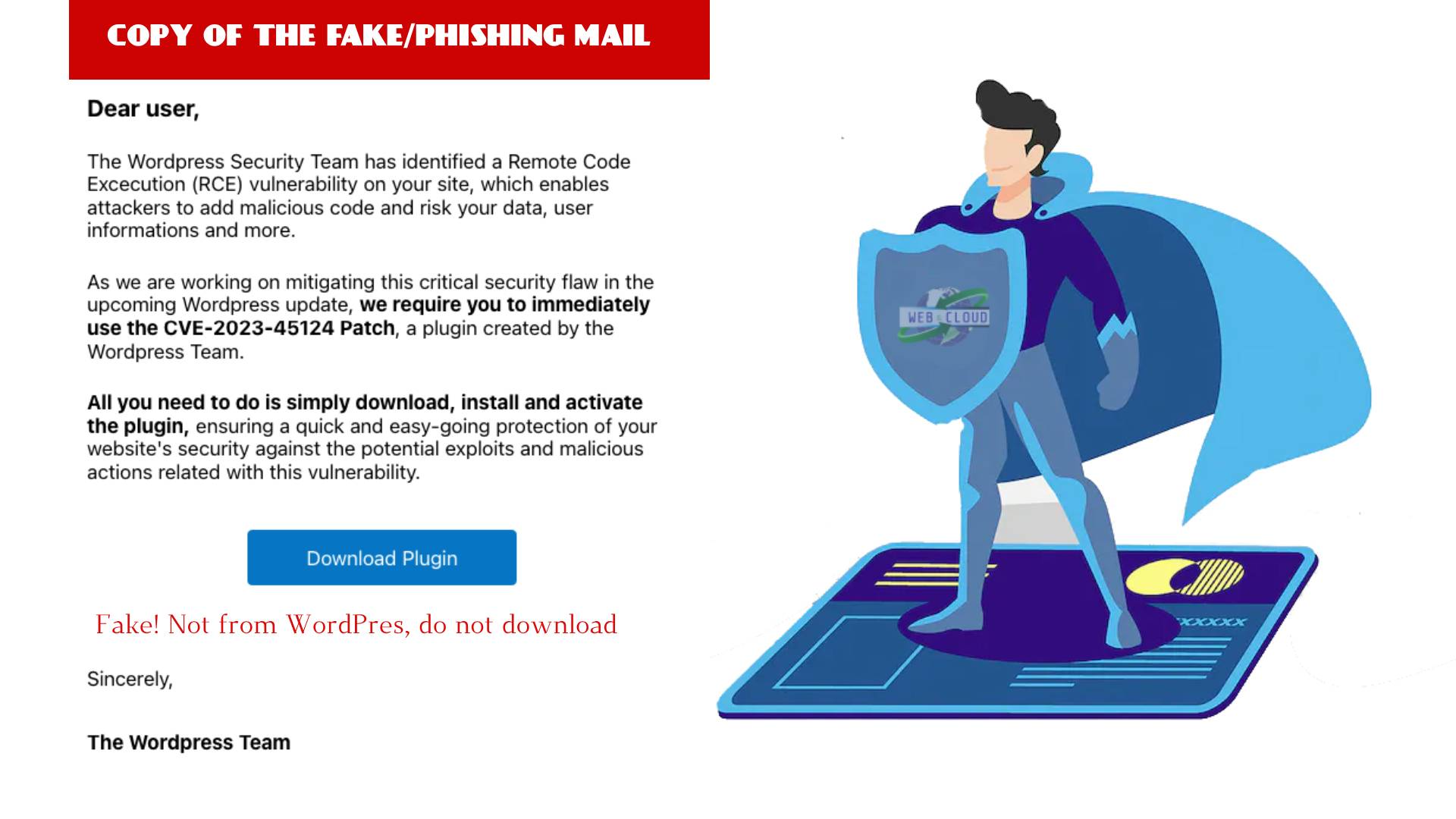
Wordfence - The Download Plugin link redirects the victim to a convincing fake landing page at en-gb-wordpress[.]org:
If the victim downloads the plugin and installs it on their WordPress site, the plugin is installed with a slug of wpress-security-wordpress and adds a malicious administrator user with the username wpsecuritypatch. It then sends the site URL and generated password for this user back to a C2 domain: wpgate[.]zip. The malicious plugin also includes functionality to ensure that this user remains hidden.
Additionally, it downloads a separate backdoor from wpgate[.]zip and saves it with a filename of wp-autoload.php in the webroot. This separate backdoor includes a hardcoded password that includes a file manager, a SQL Client, a PHP Console, and a Command Line Terminal, in addition to displaying server environment information:
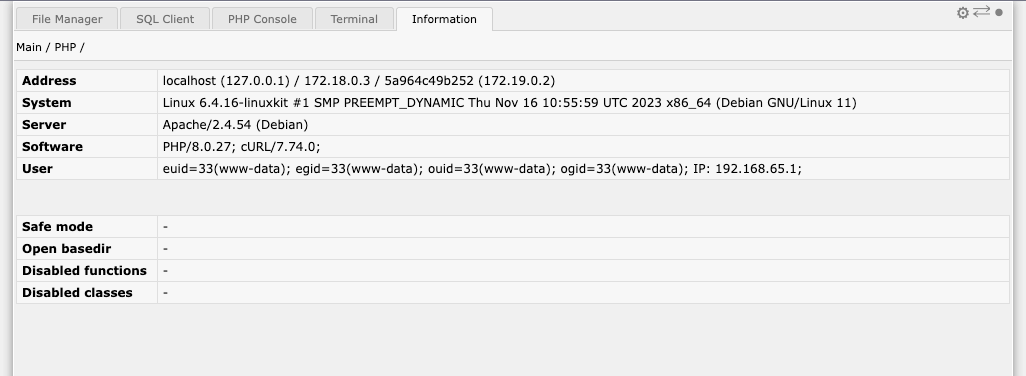
This allows attackers to maintain persistence through multiple forms of access, granting them full control over the WordPress site as well as the web user account on the server.
Indicators of Compromise:
- A
wp-autoload.phpfile in the webroot with a SHA-256 hash offfd5b0344123a984d27c4aa624215fa6452c3849522803b2bc3a6ee0bcb23809 - A plugin with a slug of wpress-security-wordpress
- A hidden administrative user with a username of
wpsecuritypatch - The following malicious domains:
en-gb-wordpress[.]orgwpgate[.]zip
Conclusion
In today’s PSA, we warned of a phishing campaign targeting WordPress users intended to trick victims into installing a malicious backdoor plugin on their site.
Our telemetry indicates that no Wordfence users are currently infected, and we have added the malicious administrator user to our known malicious usernames. Additionally, we are currently in the process of testing malware signatures to detect both the malicious plugin and the separate backdoor, which will be released to Wordfence Premium, Wordfence Care, Wordfence Response, and paid Wordfence CLI users as soon as possible. Wordfence free users will receive the same signatures 30 days later.
We will release a deep-dive analysis of the malicious plugin and separate wp-autoload.php backdoor in a future post. For the time being, be on the lookout for this phishing email and do not click any links, including the Unsubscribe link, or install the plugin on your site. If you have friends or acquaintances with WordPress sites, please forward this advisory to them to ensure that they do not install this malicious plugin.
Special Thanks to USDS expert Jonathan Kamens for bringing this issue to our attention.
Did you know that Wordfence has a Bug Bounty Program? We’ve recently increased our bounties by 6.25x until December 20th, 2023, with our bounties for the most critical vulnerabilities reaching $10,000 USD! If you’re an aspiring or current vulnerability researcher, click here to sign up.