Daolpu - Threat Actor Uses Fake CrowdStrike Recovery Manual to Deliver Unidentified Stealer
CrowdStrike Intelligence identified a Word document containing macros that download an unidentified stealer now tracked as Daolpu.

Daolpu - Threat Actor Uses Fake CrowdStrike Recovery Manual to Deliver Unidentified Stealer
CrowdStrike Intelligence identified a Word document containing macros that download an unidentified stealer now tracked as Daolpu. The document impersonates a Microsoft recovery manual.1 Initial analysis suggests the activity is likely criminal.
Technical Analysis
Lure Document
The analyzed file,
New_Recovery_Tool_to_help_with_CrowdStrike_issue_impacting_Windows.docm(SHA256 hash:
803727ccdf441e49096f3fd48107a5fe55c56c080f46773cd649c9e55ec1be61), is a Word document containing malicious macros.
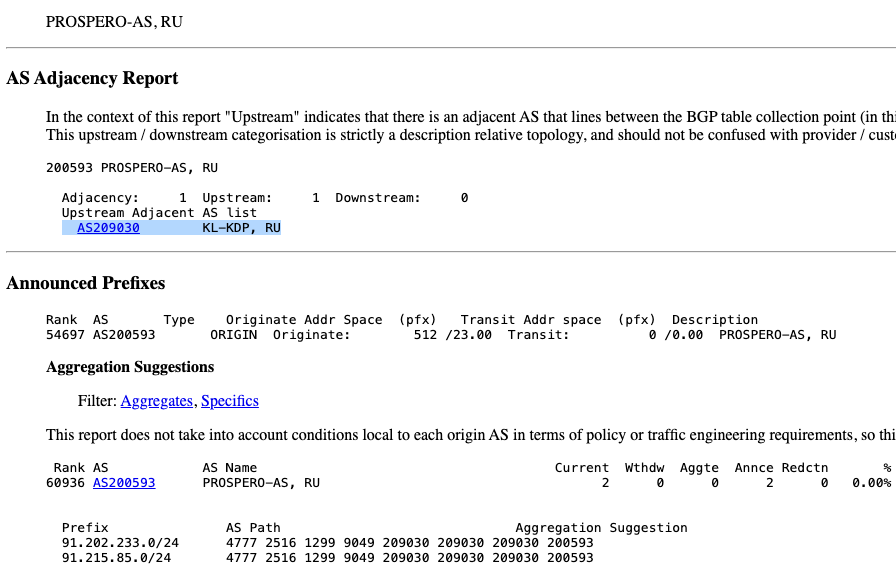
Upon execution, the macro retrieves a second-stage DLL from URL http[:]//172.104.160[.]126:8099/payload2.txt that is saved to %TMP%\mscorsvc.dll. On 22 July 2024, the URL served a file (SHA256 hash:
5eaf0f1c1d23f4372e24eb15ee969552c416a38dbc45e4f2b4af283e3bfb8721) containing a Base64-encoded DLL that, when decoded, executes the novel stealer Daolpu.
A macro decodes the DLL using the Windows utility certutil, resulting in another DLL file (SHA256 hash:
4ad9845e691dd415420e0c253ba452772495c0b971f48294b54631e79a22644a; build timestamp 2024-07-19 08:10:10 UTC). Then, the macro runs this DLL using rundll32 and calls the exported function DllMain.
Daolpu Stealer
Upon execution, Daolpu invokes taskkill /F /IM chrome.exe to kill the Chrome process. The malware then collects credentials such as login data and cookies stored in Chrome and Mozilla browsers.
The collected data is saved to %TMP%\result.txt and removed after exfiltration. The malware sends the result.txt file to the command-and-control (C2) server http[:]//172.104.160[.]126:5000/Uploadss in an HTTP POST request, which includes the system MAC address and hardcoded key Privatekey@2211#$.
Recommendations
- These recommendations can be implemented to help protect against the activity described in this report.
- Only communicate with CrowdStrike representatives through official channels and adhere to CrowdStrike support teams’ technical guidance
- Check websites’ certificates on the download page to ensure downloaded software originates from a legitimate source
- Train users to avoid executing files from untrusted sources
- Use browser settings to enable download protection that can issue warnings about potentially harmful websites or downloads
- Hunt for the file
result.txtin%TMP%, which might indicate a Daolpu infection
Appendix
YARA Rule
This YARA rule detects host-based artifacts associated with the activity described in this report.
rule CrowdStrike_CSA_240838_01 : daolpu stealer
{
meta:
copyright = "(c) 2024 CrowdStrike Inc."
description = "C++ stealer delivered via Word documents with macros impersonating CS"
reports = "CSA-240838"
version = "202407221342"
last_modified = "2024-07-22"
malware_family = "Daolpu"
strings:
$ = "C:\\Windows\\Temp\\result.txt"
$ = "D:\\c++\\Mal_Cookie_x64\\x64\\Release\\mscorsvc.pdb"
condition:
all of them
}Falcon LogScale Queries
This Falcon LogScale Query detects the activity described in this report.
// hunting rule for indicators (CSA-240838)
case { in("SHA256HashData", values=["00199b4784533a124da96be5d5e472195b0e27be15007dcbd573c0fb29941d99", "3a9323a939fbecbc6d0ceb5c1e1f3ebde91e9f186b46fdf3ba1aee03d1d41cd8", "4ad9845e691dd415420e0c253ba452772495c0b971f48294b54631e79a22644a", "5eaf0f1c1d23f4372e24eb15ee969552c416a38dbc45e4f2b4af283e3bfb8721", "803727ccdf441e49096f3fd48107a5fe55c56c080f46773cd649c9e55ec1be61"]); in("RemoteAddressIP4", values=["172.104.160.126"]) } | table([cid, aid, #event_simpleName, ComputerName])The following Falcon LogScale query detects the result.txt file with credentials in %TMP%:
// Result file with credentials for Daolpu stealer (CSA-240838)
"event_platform"="Win" | #event_simpleName = "FileOpenInfo" | FileName = "result.txt" | FilePath = /\\Device\\HarddiskVolume\d+\\Windows\\Temp\\$/Indicators of Compromise (IOCs)
This table details the IOCs related to the information provided in this report.
| Description | IOC |
| Word document SHA256 hash | 803727ccdf441e49096f3fd48107a5fe55c56c080f46773cd649c9e55ec1be61 |
| Macro download URL | http[:]//172.104.160[.]126:8099/payload2.txt |
| Second-stage file SHA256 hash | 5eaf0f1c1d23f4372e24eb15ee969552c416a38dbc45e4f2b4af283e3bfb8721 |
| Daolpu SHA256 hash | 4ad9845e691dd415420e0c253ba452772495c0b971f48294b54631e79a22644a |
| Daolpu SHA256 hash | 3a9323a939fbecbc6d0ceb5c1e1f3ebde91e9f186b46fdf3ba1aee03d1d41cd8 |
| Daolpu C2 server | http[:]//172.104.160[.]126:5000/Uploadss |
Table 1. IOCs
MITRE ATT&CK
This table details the tactics and techniques described in this report.
| Tactic | Technique | Observable |
| Execution | T1204 – User Execution | The threat actor relies on users to open the Word document |
| Credential Access | T1555 – Credentials from Password Stores | Daolpu grabs sensitive information from browsers |
| Command and Control | T1071.001 – Application Layer Protocol: Web Protocols | Daolpu exfiltrates data using the HTTP protocol |
| Exfiltration | T1041 – Exfiltration Over C2 Channel | Daolpu exfiltrates collected data to the C2 server |